What Is a Virtual Private Network (VPN)?
A virtual private network (VPN) allows users to safely connect to another network over the internet by encrypting the connection from their device. A VPN makes an internet connection more secure and offers both privacy and anonymity online.
Organizations, governments and businesses of all sizes use VPNs to secure remote connections to the internet for protection against data interception. Individuals also use personal VPNs to keep their locations private, safely encrypt data and browse the web anonymously.
What Is a Business VPN?
A business VPN is exactly what it sounds like: a VPN connection used by businesses and other professional organizations to securely connect their remote workforces and branch offices to the applications, data, tools and resources they need to do their jobs.
Many organizations use traditional perimeter security models to secure their corporate networks. Business VPNs augment perimeter security practices to give remote workers and branch office employees a virtual network through which to access the corporate network via a public or private internet connection anywhere in the world.
With a perimeter security model, a company’s IT team builds business-only security networks within the organization’s physical structures and locations, aligning the computer network security footprint to the corporate real estate footprint. This alignment between physical structures and the computer network has historically enabled network security professionals to simplify network access visibility and management.
Employees working in an organization’s headquarters directly connect to the corporate network in the corporate perimeter, eliminating the need to connect via business VPN. However, branch office employees, remote workers or staff traveling outside the secured corporate perimeter need a business VPN for secure network connectivity while they work from anywhere.
Organizations have historically relied on two business VPN connection types to keep their employees outside of headquarters secure: remote access VPN for the remote workforce, and site-to-site VPN for branch office employees.
A remote access VPN is a temporary connection between users and headquarters that is typically used for access to data center applications. This connection could use IPsec, but it is also common to use an SSL VPN to set up a connection between a user’s endpoint and a VPN gateway.
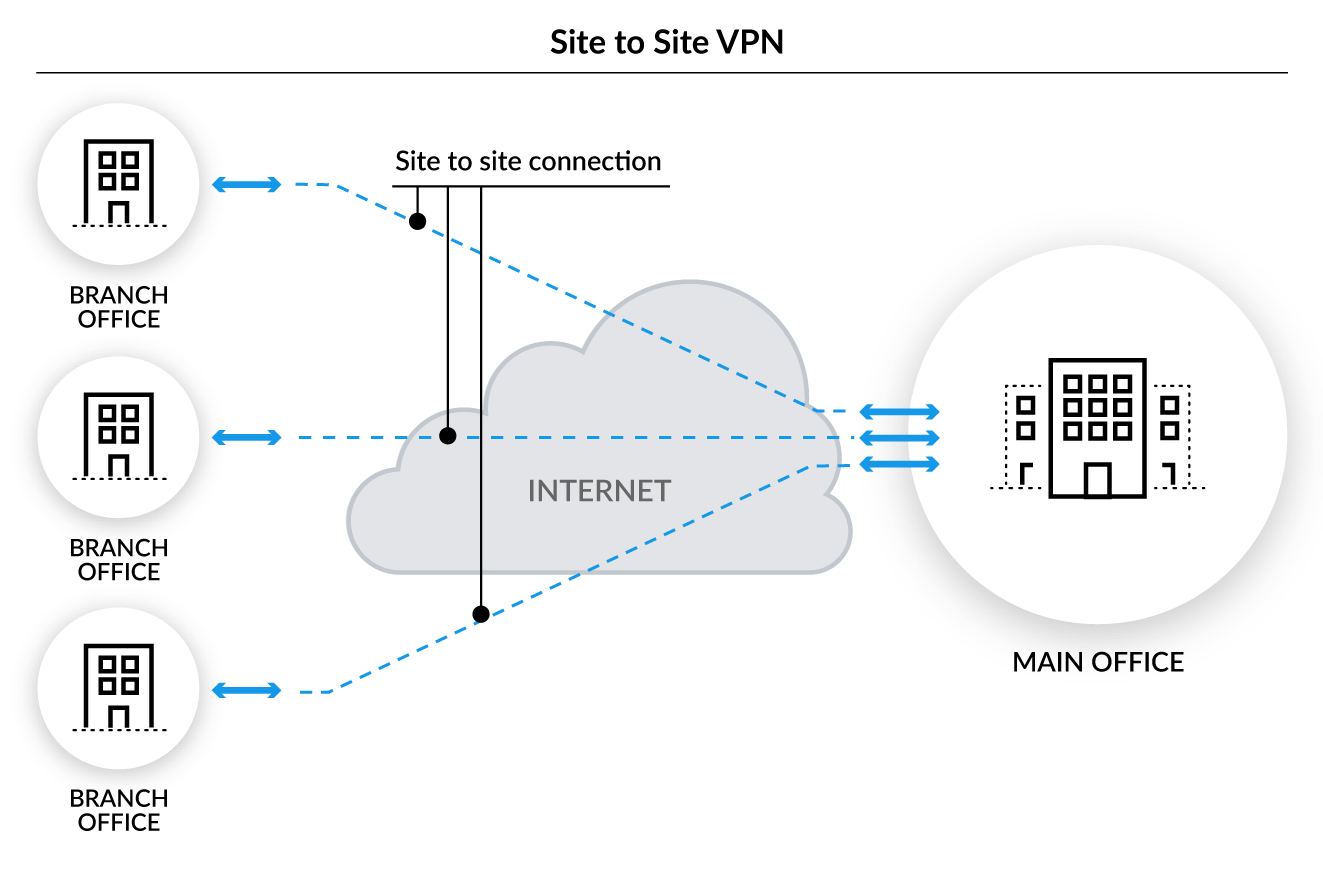
A site-to-site VPN is a permanent connection designed to function as an encrypted link between offices (i.e., “sites”). This is typically set up as an IPsec network connection between networking equipment.
Remote Access VPN
A remote access VPN gives remote users secure access to their organization’s network infrastructure. It also encrypts all traffic remote employees send and receive from the network infrastructure, enabling an organization’s remote workforce to securely access and use applications, data, tools and resources that reside in the corporate data center and headquarters.
A remote access VPN provides secure access by creating a tunnel between an organization’s network and a remote user that is “virtually private,” even when the user connects to the network via a public internet connection. Despite the public connection, the network connection is private because the network traffic is encrypted, making it unintelligible to any eavesdropper. Remote access encryption capabilities minimize organizational concerns about data tampering or interception when data travels outside the corporate network between the secure perimeter and remote workers.
However, a remote access VPN does have its limitations. With the rapid growth of remote workforces and cloud-based applications, organizations are finding remote access VPN is neither optimized for the cloud nor secure.
Remote access VPN is typically deployed in a hub-and-spoke architecture, with users sitting in spokes of various lengths depending on their distance from the hub—the internal data center. Distance degrades performance and introduces issues with latency, but this is nevertheless the optimal architecture for data center applications because the goal is to reach the hub. To compensate for the networking problems with remote access VPN, organizations typically make compromises that have negative security implications.
Organizations with a remote workforce need the proper network security architecture and solutions to optimize access to the data center, the internet, and applications in public, private and hybrid clouds.
Site-to-Site VPN
Unlike a remote access VPN, which connects individual devices or users to an organization’s corporate network, a site-to-site VPN is a connection between two or more networks, such as a corporate network and a branch office network. Many organizations choose site-to-site VPNs so they can use an internet connection for private traffic rather than private multiprotocol label switching (MPLS) circuits.
Site-to-site VPNs are frequently used by companies with multiple offices in different geographic locations that need ongoing access to and use of the corporate network. With a site-to-site VPN, a company can securely connect its corporate network with its remote offices to communicate and share resources with them as a single network.
Business VPN vs. Personal VPN
The primary difference between personal and business VPN is whether users connect their devices to a corporate network or a personal network. If users wanted to access employer-related applications, resources or data, they would need to connect to the VPN maintained by their employer, typically from their employer-provided laptops, mobile phones or other managed devices. They could also connect to the corporate network from their personal laptops or devices as long as those devices have a VPN agent deployed on them to facilitate this connection.
Individuals use personal VPNs for a private network connection that enables them to access applications, resources and data based on their own interests or needs. In many cases, individuals use personal VPNs to keep their internet browsing private when connecting online with an internet service provider (ISP) or public Wi-Fi. In some geographies, individuals use personal VPNs to access websites or content that may be blocked on the public internet in their country or region. Generally speaking, personal VPNs aren’t as widely used as corporate VPNs, with approximately one-fourth of all internet users accessing online content with a personal VPN.
Business VPN Limitations
Despite their popularity, both business VPN connection types – remote access VPN and site-to-site VPN – have security deficiencies, due primarily to the limitations of the perimeter security model when it comes to providing comprehensive protection.
The combination of an increased remote workforce population with greater adoption of cloud-based infrastructure and applications – including those for cybersecurity – is making perimeter-based cybersecurity techniques cumbersome and increasingly insufficient if implemented without other cybersecurity tools. Organizations need to look beyond VPN capabilities to ensure devices connecting to the corporate network from outside the corporate perimeter – and the data moving between the devices and the network – remain secure.
VPN Speed
Internet speed is the primary determinant of VPN speed. VPN speed cannot be any faster than the internet connection between a device to a corporate network.
After internet connection speed, VPN technology itself is the most important determinant of VPN speed. Companies build VPN technology that mainly focuses on data security and privacy, and – depending on how each company encrypts and authenticates VPN traffic – VPN speed can be reduced if the encryption and authentication technologies increase the data size, send it through multiple checkpoints, or redirect traffic as it goes through the VPN tunnel.
Another factor impacting VPN speed is the amount of data traveling over the VPN connection at one time. For instance, VPN speed may be slower if someone participates in a video call (something that sends a lot of data back and forth across the network) compared to a less data-intensive activity, such as accessing and saving a text-based document on a corporate file server.
VPN Security
VPN security enables business VPN users to maintain their privacy and secure their data when connected to the internet. Organizations ensure VPN security for their remote workforce by using remote access VPNs, with site-to-site VPNs for their branch offices.
Enterprise Network Security Solution Alternatives
There are better enterprise network security solutions than remote access VPN available for organizations to connect their remote workforces to the corporate network. Organizations can also take advantage of SD-WAN solutions rather than rely on site-to-site VPN to secure their branch offices. With next-generation SD-WAN, companies can get speed, lower total cost of ownership (TCO), and a rich set of security and network services from the cloud.
Cloud Network Security
With the increase in the remote workforce and cloud-based applications, more organizations require cloud network security rather than business VPNs to protect their networks. A secure access service edge (SASE) solution helps organizations embrace cloud and mobility by providing networking and network security services from a single cloud-based solution.
With the common framework a SASE solution provides, organizations can gain the cloud network security they need as well as simplify management, get consistent visibility, and maximize network protection across users, devices and applications, no matter their location.
